What is Outdoor WiFi or Long-Range WiFi Network?
What is Outdoor WiFi or Long-Range WiFi Network?
Outdoor WiFi are low-cost setups that can help improve your internet connection throughout your property; This set up gives you the ability to access a network from miles away - whether it’s to share the internet connection with another building or simply extend the WiFi signal outside.
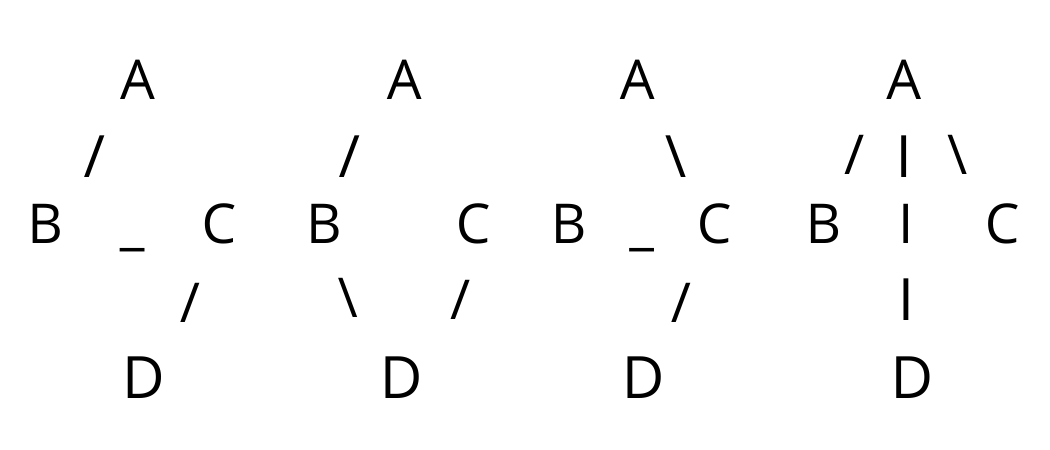
To provide outdoor WIFI to an area adjacent a building,
there are two approaches:
1) exterior, weatherproof, purpose-built access points,
mounted on the outside of the building.
2) interior access points mated with exterior antennas.
The AP is inside the building; the antenna is outside.
Often, you will choose an AP or antenna with a sector radiation pattern that directs coverage away from the building and out into an open space.
The AP or sector antenna might create a 30, 45, 60, 90, or 120 degree horizontal wedge. The narrower the antenna pattern, more concentrated the power from the transmitter. This concentration is expressed as the antenna's gain factor. An antenna with a narrow sector pattern can provide service for many miles over a smaller coverage area.
In the US, the effective radiated power output is limited to 100 milliwatts, by law. When you pair an antenna with an access point, you will have to program a gain factor for the antenna. This will be provided by the antenna manufacturer. The gain value tells the transmitter to reduce output power to remain within the law.
Antenna extension cables and connectors can cause losses between the transmitter and the antenna. With long antenna cables, you may have to reduce the programmable gain to make up for the losses. It is better to extend the Cat5e or Cat6 data cable that provides data and power to the access point than to extend the antenna leads.
When choosing a location for an exterior antenna or AP, it is best that there be line-of-sight between the antenna and the area to be covered. Trees and other structures will attenuate radio signals, particularly for the 5 GHz bands.
It is also very important that the near-field of the signal be
unobstructed. Roof edges, building overhangs and corners can interfere with the radiation pattern.
Picture a pebble dropped into the water. Ripples will radiate evenly in all directions. Now, picture the same pebble dropped into water with rocks. The ripple pattern will be disturbed by the reflections from the obstructions. We want to avoid the same kind of reflections with WiFi.
To cover an open space with many access points, such as a quadrangle, it is better to mount the antennas high and aim them downward, toward the ground. This is the same approach that one would take if installing outdoor lighting, careful to light each area independently.
To provide WiFi to locations far away, a wireless bridge or mesh may be desired. An access point located on a building can create a back-haul link to a distant access point or access points.
When there is one access point at the far end of the back-haul link, we call this a point-to-point connection or bridge. When there are several, we call this point-to-multipoint or mesh. The distant access points may provide local service as if they were wired.
Often, with a dual-radio access point, one radio is used for the back-haul network. The other is used to provide WiFi access. Sometimes, you will use a high gain antenna for the back-haul radio and an omni-directional antenna for user WIFI. You may also let down a wired connection for a camera or switch.
There must be electrical power available at the far end of the link. This can be hard-wired AC power or provided by a power injector depending on the AP and the application. A typical access point plus camera installation will include two power injectors--one for the AP and one for the camera.
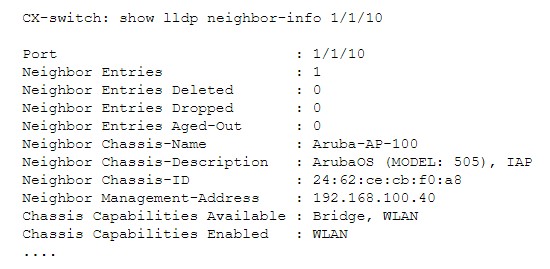
In an WiFi infrastructure, APs that form the bridge or mesh are managed by a wireless controller or cloud just as the campus APs are. Sometimes, instead, an inexpensive third-party bridge can be used to extend the campus network. Devices located at the far end, including access points, will not be aware of the third-party wireless bridge.
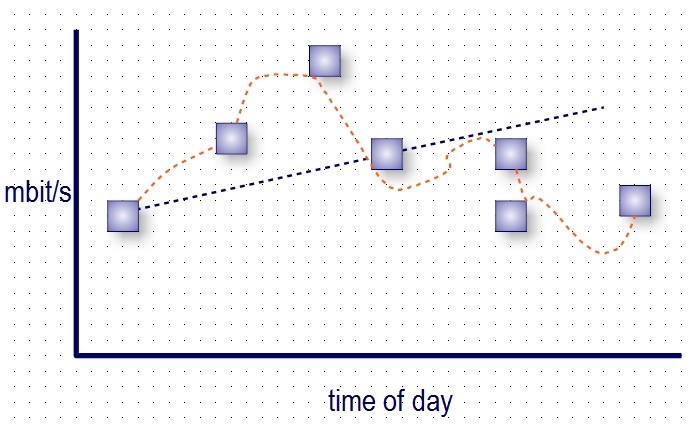
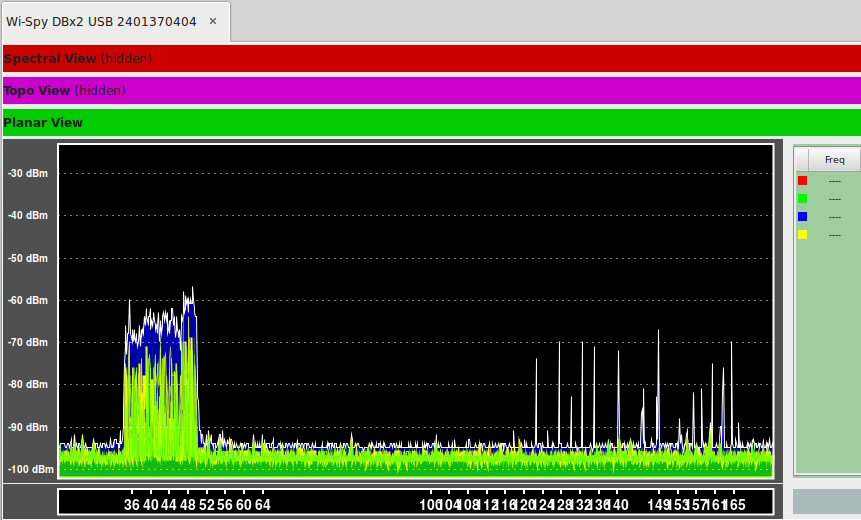
A typical bridge or mesh configuration will use a 5 GHz link for back-haul and 2.4 GHz for local service. The expected speed in a nearby, line-of-sight application is often just over 100 mbit/S.
Bridge and mesh products that use 24 GHz or 60 GHz radios are also available. These feature back-haul speeds that in the 1 gbit/S range. The wavelength of a 60 GHz signal is just 5mm, which is less than the width of a large raindrop or a snowflake. Because of this, 24 GHz and
60 GHz transmissions are subject to 'fade' or failure in rain, snow or fog. For this reason, 60 and 24 GHz bridges are often packaged with 5 GHz fall-back radios.
A bridge built from 900 MHz radios can penetrate trees and weather much better than a 5 GHz radio, but with much narrower channel width, measured in 100s of kbits/S.
Local outdoor coverage, bridges or meshed links--Atlantic has been providing commercial WiFi for 15 years. Call us for your next project.
- Kevin Dowd
 What is Outdoor WiFi or Long-Range WiFi Network?
What is Outdoor WiFi or Long-Range WiFi Network? There is a limit to the number of bitcoins--21 million in total, with about 2 million left to be mined. Presently, there are about 900 new bitcoins per day. As more are found, the hash target becomes increasing harder to hit and it becomes asymptotically harder to find additional bitcoins. It will be the year 2140 before the last one is finally found. There's investment and reward in the effort: Russia just took delivery of a 70 MW crypto mining farm. It is said that almost 65% of the cryptomining resources are in China. Bitcoin broke $50,000 on Tuesday. Elon Musk bought $1.3 billion in bitcoin a couple weeks ago, when it was already over $40,000. Projections are for $500,000 per bitcoin.
There is a limit to the number of bitcoins--21 million in total, with about 2 million left to be mined. Presently, there are about 900 new bitcoins per day. As more are found, the hash target becomes increasing harder to hit and it becomes asymptotically harder to find additional bitcoins. It will be the year 2140 before the last one is finally found. There's investment and reward in the effort: Russia just took delivery of a 70 MW crypto mining farm. It is said that almost 65% of the cryptomining resources are in China. Bitcoin broke $50,000 on Tuesday. Elon Musk bought $1.3 billion in bitcoin a couple weeks ago, when it was already over $40,000. Projections are for $500,000 per bitcoin.